Cybersecurity vendor risk management (VRM) is notoriously difficult. Security teams need to know when their vendors experience a security incident, but they often lack visibility into supply chain threats.
Many companies only learn about a security incident when the vendor notifies them. Meanwhile, as soon as threat actors know about a vulnerability, they start acting on that knowledge, which leaves you increasingly vulnerable.
Additionally, not every vulnerability affects your security, and not every vulnerability affects your security equally. You need meaningful, real-time insight into the high risk threats facing your company and supply chain vendors.
With Feedly for Cybersecurity, you can create Feeds tailored to your technology stack and supply chain, including hardware, software, and firmware for streamlined monitoring enabling proactive remediation. Unlike keyword matching, Leo uses artificial intelligence to recognize key information so that you never miss important information. You can also share this focused risk intelligence with industry peer groups like Information Sharing and Analysis Centers (ISACs) or team members using email, messaging applications, and the Feedly API.
From a proactive monitoring perspective, the power of using Feedly is to actually inform you of breaches before anyone else knows.”
Reduce the noise with a Feed focused on your supply chain risks
Threat researchers use many different intelligence tools. Whether getting data from a managed services provider (MSP), setting news alerts, following social media, or collecting cybersecurity newsletters, the time and information overload is overwhelming. To reduce noise, you might be setting alert emails to come in once a day. However, filtering through all those emails is time-consuming and overwhelming. On top of this, once you find a nugget of valuable information, you need to do independent research to get the details you need to protect your company, and you need them quickly.
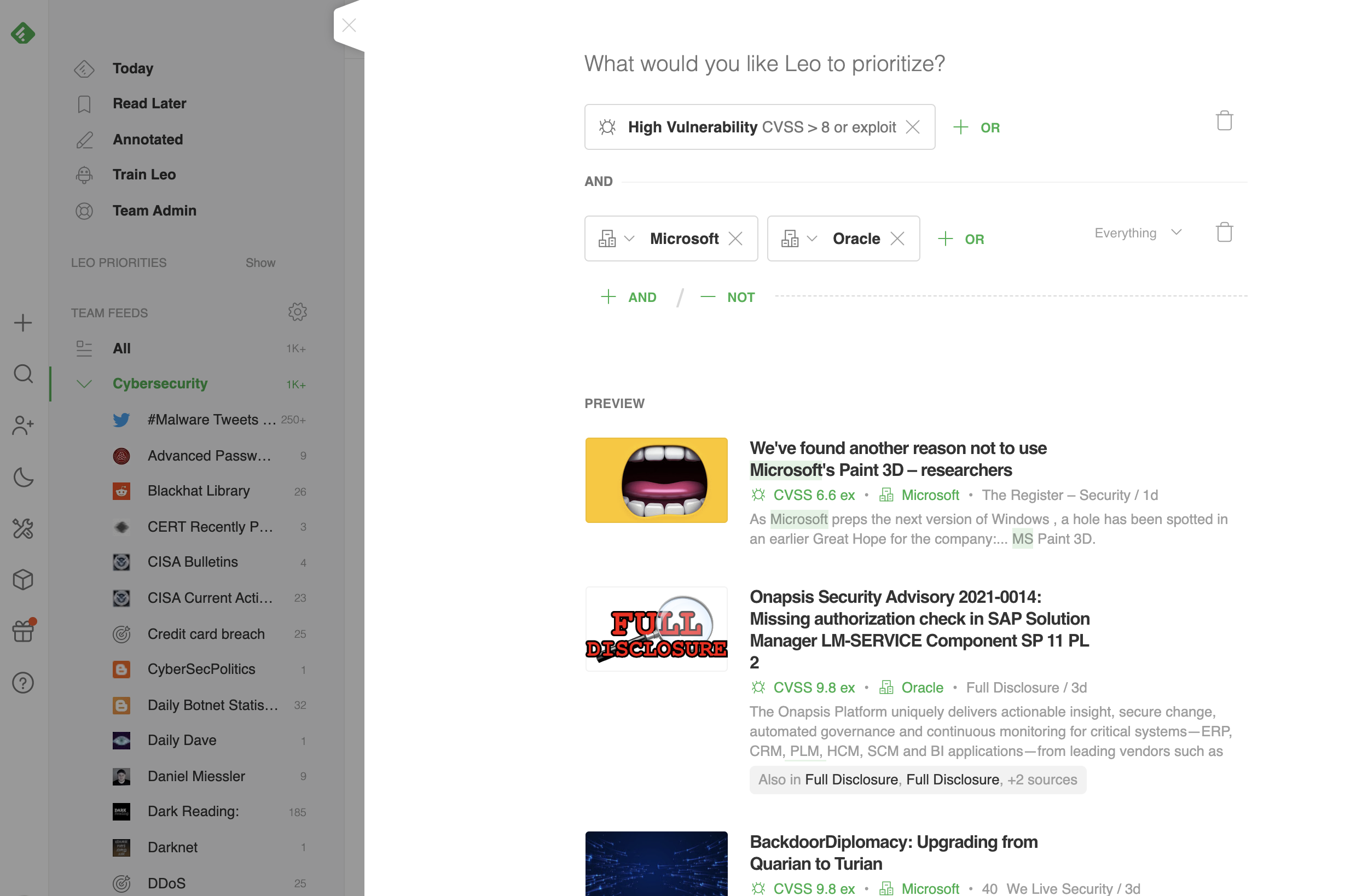
We trained Leo to understand cybersecurity and critical vulnerabilities to synthesize all the information you need. Training Leo by setting Priorities based on your vendor list lets you teach him to focus on only what you need to secure your environment information. Priorities help you teach Leo about the risks unique to your supply chain, whether it’s hardware, software, or a non-technology business partner.
By customizing your Feed using Leo and Priorities, you fine-tune your threat intelligence and build visibility around risk criticality.
Creating dashboards around the threat intelligence you need
Leo knows cybersecurity, and you can teach Leo to know your supply chain risk, too. With the LEO CVE Dashboard, you get at-a-glance, real-time visibility into:
- CVSS score and vector string
- CWE
- Affected systems, including vendor advisories
- Exploit information
- Patches
- Associated malware families
- Associated threat actors
- Awareness graph
- Number of Web and Social Media mentions, including Twitter and Reddit
Teach Leo which vendors to track
More than just reducing the noise, Leo streamlines threat intelligence research with visualizations that help you prioritize your organization’s risk.
In your Today feed, you’ll see a list of recent, critical vulnerabilities for at-a-glance visibility into new threats facing your technology stack.
When you click on the vulnerability, you’ll see a color-coded awareness graph for at-a-glance visibility into what people are saying about a specific CVE.
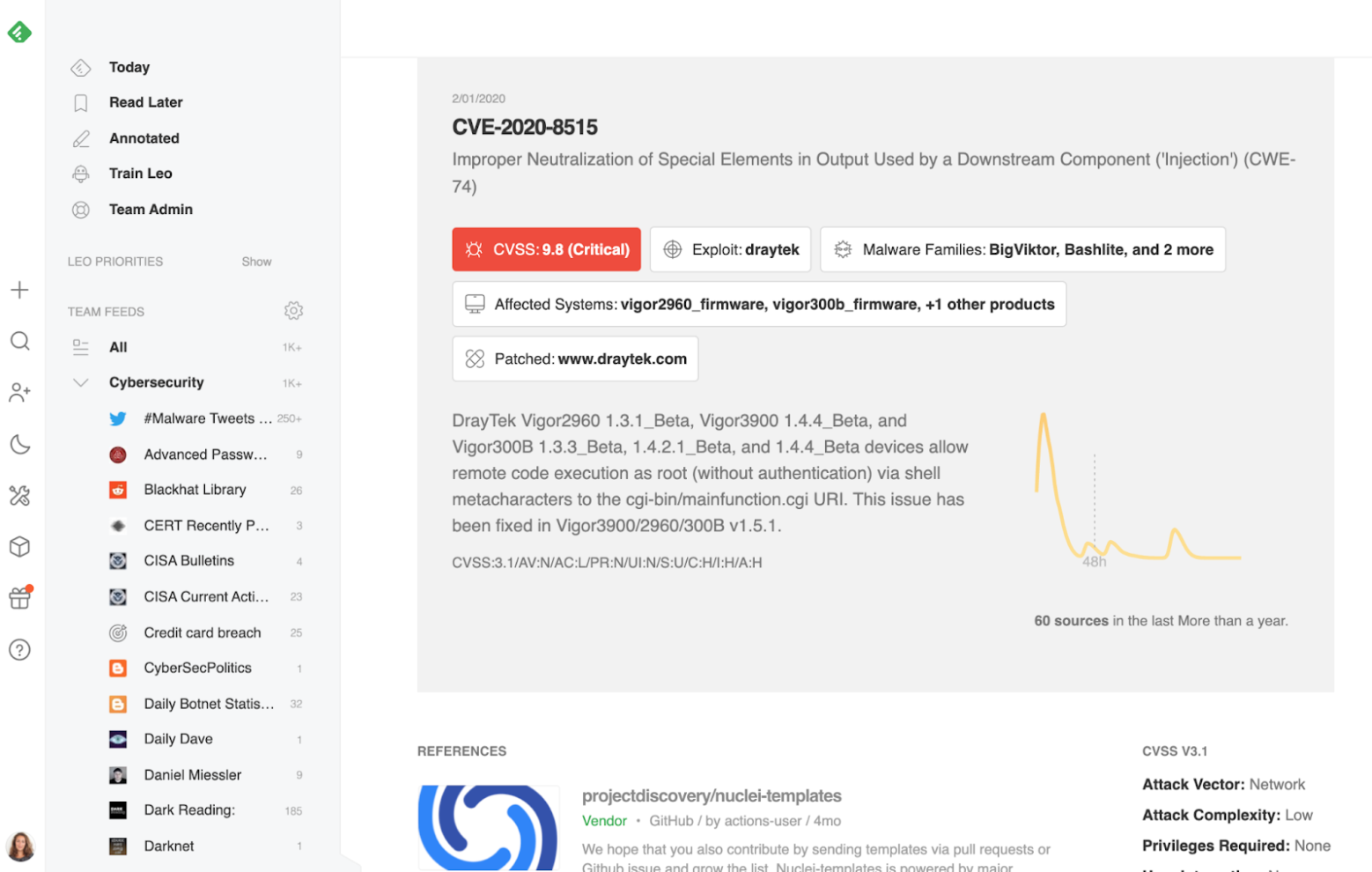
The clickable boxes direct you to more information about the vulnerability, including:
- threat actors
- malware families
- affected systems
- available patches
By training Leo and setting Priorities, you get focused threat intelligence giving you the visibility you need and enabling you to respond more rapidly to new threats. This visibility improves key cybersecurity metrics like reducing mean time to detect (MTTD) and mean time to remediate (MTTR).
For example, one customer in the energy industry used Priorities alerting them to a new vulnerability so that they could patch the problem within two days, rather than having a security weakness that could lead to a data breach. .
Set Priorities to focus your feed
Setting Priorities to teach Leo about your critical supply chain risks is an intuitive process.
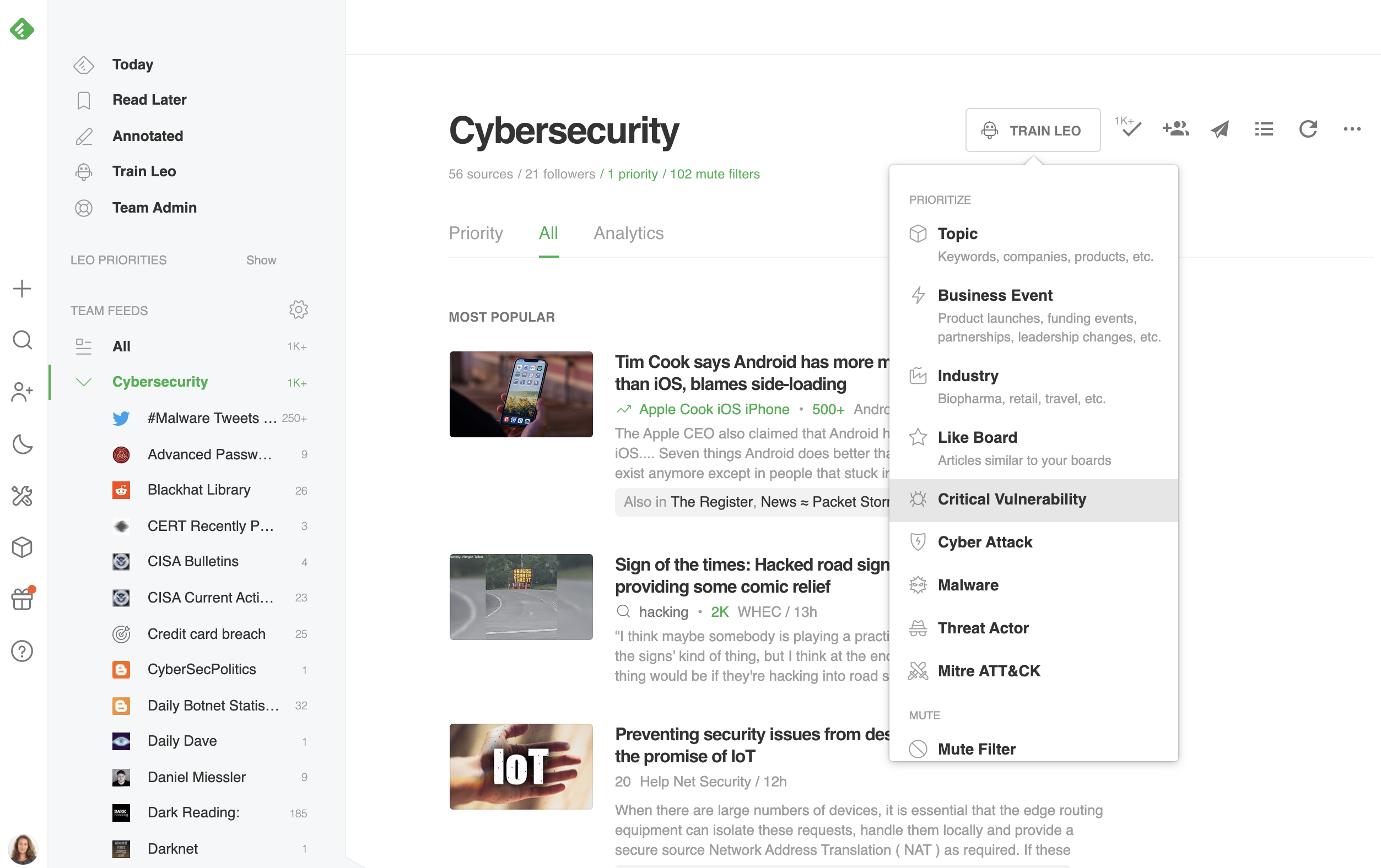
Start by defining the level of CVE criticality you care about most. If you need more than one Feed so that you can look at High Risk and Moderate Risk CVEs, you can do that, too.
Now, personalize that Feed to your current critical technologies and business partners. You can add any as you want, including business applications, messaging apps, or any other critical vendors that your team wants to monitor. To add more terms and risks, just click ‘OR’ and add each new term.
Use the Feedly Cybersecurity API to prioritize remediation activities
Once you have the information, you need to share it across the team to remediate risk. The Feedly Cybersecurity API gives you a way to share information and reduce MTTR.
Feedly supplies access tokens so that you can send the aggregated CVE/CVSS/Exploit information using JSON format. By translating to JSON, Feedly gives you a way to align your threat intelligence with your event log data to enhance correlation and analysis. With our API, you can connect your threat intelligence into any Security Information and Event Management (SIEM) or Security Orchestration, Automation, and Response (SOAR) solution that uses these integrations. For example, the Feedly API adds metadata to articles including associated malware families and threat actors, entities mentioned, and MITRE tactics and techniques., With all the information you need in a single location, you bring together the technical information and threat intelligence together for full visibility into all risks.
Finally, you can forward critical security data directly to your ticketing application, like Jira, and build it directly into your team’s workflow. This capability saves time since you don’t need to jump between different windows and applications.
“Leo makes Feedly unique because he allows us to build queries and thus create our own Feeds. This gives us the ability to focus on the articles we WANT to read.”
Try Feedly for Cybersecurity
Feedly for Cybersecurity streamlines supply chain threat research to help you more rapidly respond to emerging threats.





